Disk Forensics
6[84]45 Week 2
Good Faith Policy
“These courses expects a high standard of professionalism from its students with regard to how security testing is conducted. We expect all students to act in good faith at all times […]”
TL;DR Don’t be mean
Report 1
Have a look at the guidelines here
- You’ve been given a case on Caelus Engineering
- You’re provided with a disk image of a laptop
- You need to analyze this image and answer questions
- Then present your findings in the format of a report
Discussion
Choose one of the principles of Handling Digital Evidence and explain its importance in a practical sense
What could go wrong if it isn’t followed?
What is an ethical repercussion you could imagine of not adhering to this principle?
What is a disk?
Disk Acquisition
Demo: disk acquisition
- Physical vs logical acquisition
- Raw images and E01 files..
Files
Drive Structure
- sector: smallest storage unit of a drive (usually 512B)
- clusters: groups of sectors
- partition: an allocated segment of a drive
- volume: logical container in a partition
- file system: data structure for organisation of files
- unpartitioned space: unassigned drive space
Hidden Items
Where could you look for hidden information on a drive?
Hidden items
- Where to look for hidden information on a drive?
- Hidden partitions (e.g. modified PT)
- Unallocated space
- Slack (drive and volume)
- HPA - Host Protected Area
- DCO - Device Configuration Overlay
Read more here
SSD vs HDD
Would it be harder to carve files on a SSD or HDD, why?
Files
What is a file?
- The actual data itself
- Information about the data (metadata)
- (e.g. name, owner, time of creation/access, etc)
- Location of the data
file
What does the file command in Linux does?
Does it just look at the extension?
File Signatures
The first few bytes of a file indicate its “type”
- aka “magic bytes”
filejust reads these bytes (a MIME-type check)- Read more here
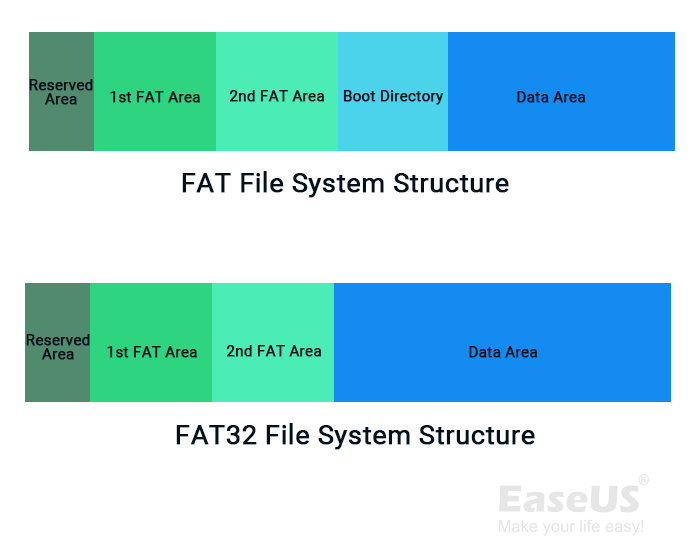
File Systems
- FAT32
- NTFS
- ext
n
Why do we need file systems?
FAT32
- File Allocation Table (FAT)
FAT: linked list of statuses of all clusters
| status | indicates |
|---|---|
0x?0000000 | free cluster |
0x?0000002 | cluster in use (value is next cluster for file) |
0x?FFFFFFF | cluster in use EOF marker |
Deleted files
- What happens to file contents when a file is deleted?
- What else happens (specifically in FAT?)
Deleted files
What happens to file contents when a file is deleted?
- Data is kept
What else happens (specifically in FAT?)
- First character in filename changed to
0xE5 - All clusters in FAT replaced with
0x00
- First character in filename changed to
Why are these important
demo: undeletion
demo: file recovery
- e.g. R-Studio, scalpel, photorec, recoverjpg, WinfrGUI
NTFS
$MFT (DEs of NTFS)
$BITMAP (FATs of NTFS)
Everything is a file™
Everything in a file is an attribute
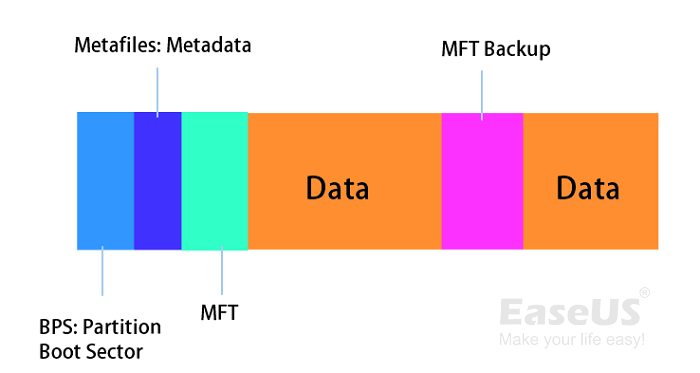
Extents
- Similar to Cluster Runs
- A contiguous area of storage reserved for a file
Alternative Data Streams
- Also a file attribute
- Is referenceable as a file path
- Not honoured by other file systems
- Originally used to provide compatibility with Macs
- These days.. used to hide malware lol
Read more here
Deleted files
- What happens for NTFS
Deleted files
- What happens for NTFS
$MFTmarks$FILEentry as available$DATAattribute read,$BITMAPupdated to show cluster runs no longer used- Nothing is wiped/deleted from
$MFTor clusters
Until the FILE entry is overwritten, the data is still there
Why don’t we delete files straight away???
demo: usb capacity spoofing
Disk Acquisition, again
- Physical vs logical acquisition
- Raw images and E01 files..
Anti-forensics
- Physical destruction
- Secure wipe (zero, random)
m57 #1
Investigation